Author/Source: Krebs on Security See the full link here
Takeaway
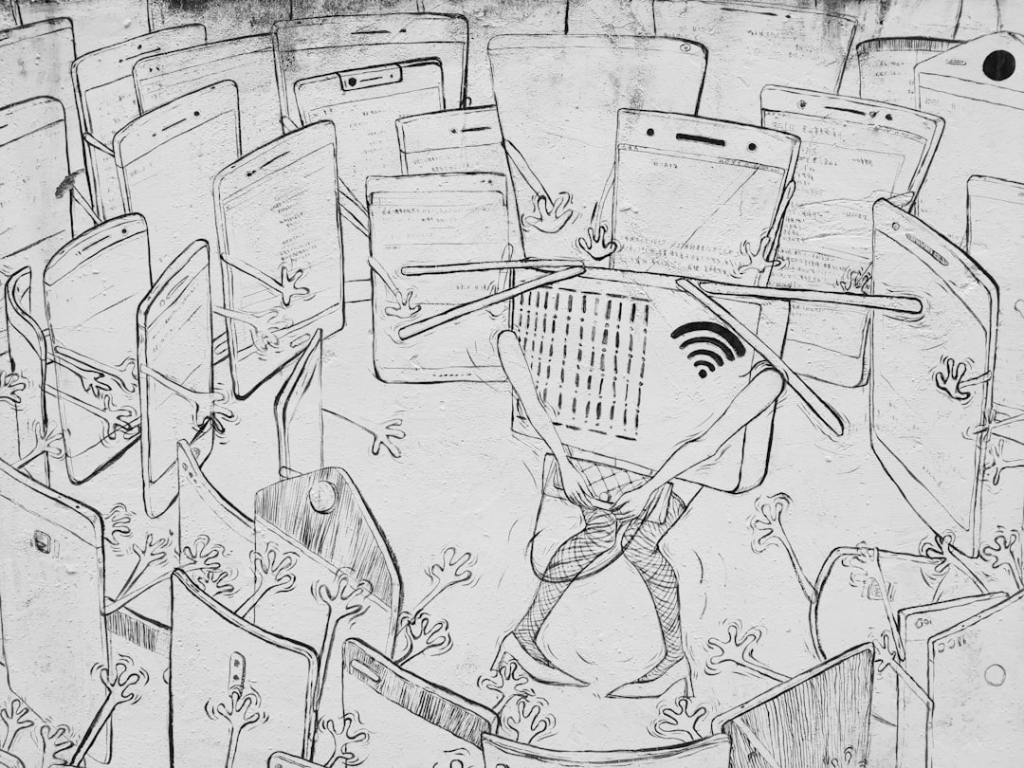
The Kimwolf botnet, which infects internet-connected devices, recently overwhelmed the I2P anonymity network. This disruption occurred because the botnet operators tried to join hundreds of thousands of infected devices to I2P as a backup communication method, causing widespread outages for legitimate users.
Technical Subject Understandability
Intermediate
Analogy/Comparison
This situation is like trying to have a private conversation in a small room, but then hundreds of thousands of uninvited people suddenly flood in, making it impossible to hear anyone or move around.
Why It Matters
Botnets like Kimwolf can disrupt vital online services and privacy networks. For example, the Kimwolf botnet caused the I2P network to operate at half its normal capacity, preventing legitimate users from communicating anonymously and securely.
Related Terms
Botnet, Internet of Things (IoT), Distributed Denial-of-Service (DDoS), The Invisible Internet Project (I2P), Sybil attack
Jargon Conversion
Botnet: A network of infected computers or devices controlled by a single attacker. Internet of Things (IoT): Everyday devices like smart TVs or routers that connect to the internet. Distributed Denial-of-Service (DDoS): An attack that overloads a service with too much traffic from many sources, making it unavailable. The Invisible Internet Project (I2P): A special network designed to keep online communications private and anonymous. Sybil attack: A type of attack where one person creates many fake identities to disrupt a network.
Leave a comment